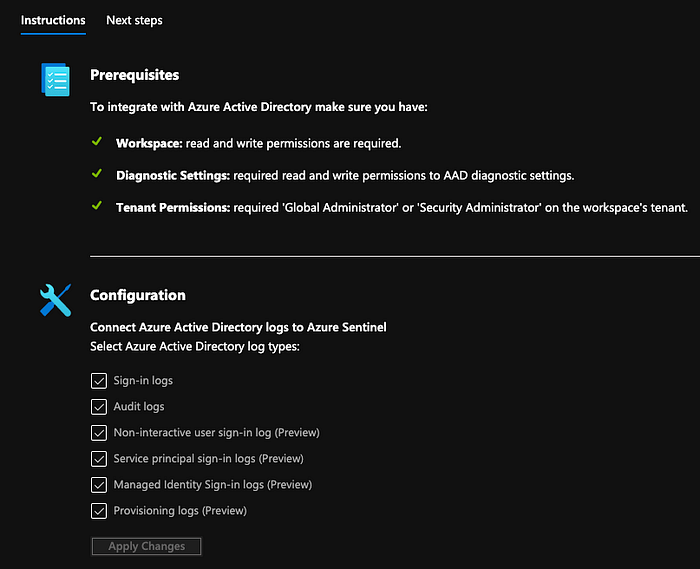
Azure Sentinel is Microsoft’s new cloud-native Security Incident and Event Management (SEIM) tool. If you use Azure AD (AAD) for your single-sign on (SSO) identity provider (IDP) for your SaaS apps, those AAD logs will seamlessly integrate with Azure Sentinel with the check of a box.
However, if you’re using Okta as your IDP, this can also natively integrate very easily with Sentinel so you get your identity logs into your SIEM. To get started, first go to your Okta Admin portal and navigate to Security -> API -> Tokens. Create a token (call it something like AzureSentinelAPI or whatever your naming convention is). Make sure you copy the API to a safe location.
Navigate to Azure Sentinel and search for the Okta connector and open the connector page.

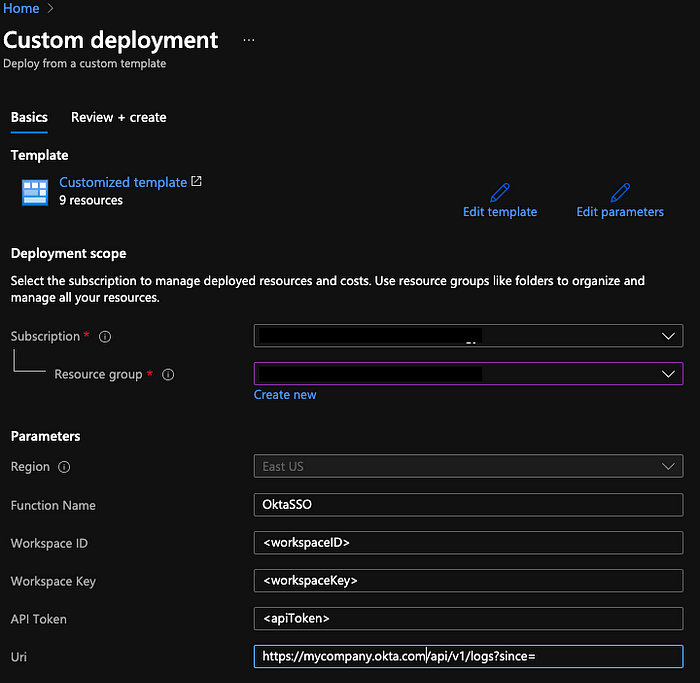
Once you open the connector page, there are two options on how to deploy the connector. The first is an automated deployment of an Azure Resource Manager (ARM) template. This is the easiest method. If you want, you can manually deploy the Azure functions separately as well.
Following Options 1, click the Deploy to Azure button. Pick the subscription and resource group that your Azure Sentinel deployment is home to. Fill in your Workspace ID and Workspace Key for your Azure Sentinel Workspace. Fill in the API token from Okta. Change the URI under <Okta domain> to your Okta URL.
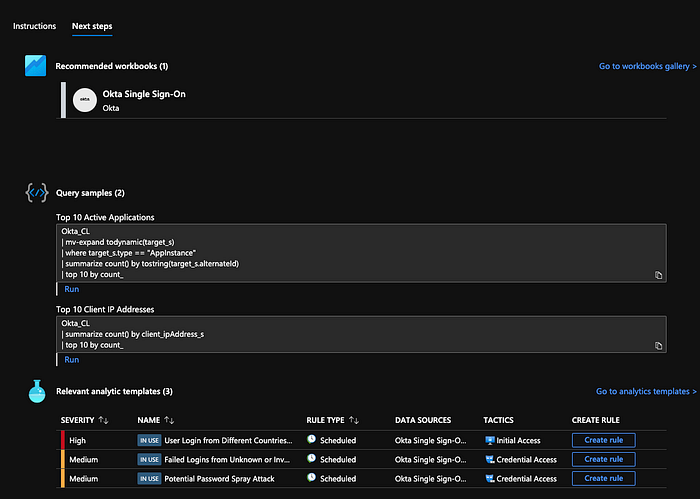
Deploy and you’re done! Under next steps, you can run the query samples to make sure your logs are coming in. You should also create the analytic rules to get notified whenever there’s a security alert of concern.
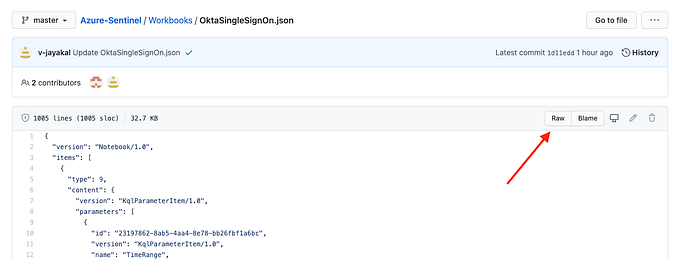
Finally, in the Azure Sentinel Github, there’s a very handy workbook that you can import into your environment to get a rich table of data. Use the provided link and click on “Raw.”
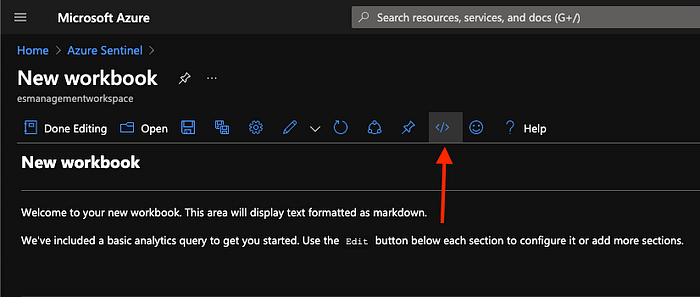
Copy and paste the text and go to the Azure Sentinel console and select “+Add workbook” under Workbooks.

Click “Edit” and select Advance Editor.
Paste the Github text over the sample text in the Gallery Template and save the workbook. Done! You’ve successfully onboarded Okta to Azure Sentinel and configured a workbook to have a rich layer of data to display for you to comb through.
Let me know if you have any questions!
